Cyberark PAS module
editCyberark PAS module
editThis functionality is in beta and is subject to change. The design and code is less mature than official GA features and is being provided as-is with no warranties. Beta features are not subject to the support SLA of official GA features.
This is a module for receiving CyberArk Privileged Account Security (PAS) logs over Syslog or a file.
The ingest-geoip Elasticsearch plugin is required to run this module.
Read the quick start to learn how to configure and run modules.
Configure the module
editYou can further refine the behavior of the cyberarkpas module by specifying
variable settings in the
modules.d/cyberarkpas.yml file, or overriding settings at the command line.
You must enable at least one fileset in the module. Filesets are disabled by default.
audit fileset settings
editThe audit fileset receives Vault Audit logs for User and Safe activities over the syslog protocol.
Vault configuration
editFollow the steps under Security Information and Event Management (SIEM) Applications documentation to setup the integration:
-
Copy the elastic-json-v1.0.xsl XSL Translator file to
the
Server\Syslogfolder. -
Sample syslog configuration for
DBPARM.ini:
[SYSLOG] UseLegacySyslogFormat=No SyslogTranslatorFile=Syslog\elastic-json-v1.0.xsl SyslogServerIP=<INSERT FILEBEAT IP HERE> SyslogServerPort=<INSERT FILEBEAT PORT HERE> SyslogServerProtocol=TCP
For proper timestamping of events, it’s recommended to use the newer RFC5424 Syslog format
(UseLegacySyslogFormat=No). To avoid event loss, use TCP or TLS protocols instead of UDP.
Filebeat configuration
editEdit the cyberarkpas.yml configuration. The following sample configuration will accept TCP
protocol connections from all interfaces:
- module: cyberarkpas
audit:
enabled: true
# Set which input to use between tcp (default), udp, or file.
#
var.input: tcp
var.syslog_host: 0.0.0.0
var.syslog_port: 9301
# With tcp input, set the optional tls configuration:
#var.ssl:
# enabled: true
# certificate: /path/to/cert.pem
# key: /path/to/privatekey.pem
# key_passphrase: 'password for my key'
# Uncoment to keep the original syslog event under event.original.
# var.preserve_original_event: true
# Set paths for the log files when file input is used.
# var.paths:
For encrypted communications, follow the
CyberArk documentation
to configure encrypted protocol in the Vault server and use tcp input with var.ssl settings in Filebeat:
- module: cyberarkpas
audit:
enabled: true
# Set which input to use between tcp (default), udp, or file.
#
var.input: tcp
var.syslog_host: 0.0.0.0
var.syslog_port: 9301
# With tcp input, set the optional tls configuration:
var.ssl:
enabled: true
certificate: /path/to/cert.pem
key: /path/to/privatekey.pem
key_passphrase: 'password for my key'
# Uncoment to keep the original syslog event under event.original.
# var.preserve_original_event: true
# Set paths for the log files when file input is used.
# var.paths:
Configuration options
editVariable settings
editEach fileset has separate variable settings for configuring the behavior of the
module. If you don’t specify variable settings, the cyberarkpas module uses
the defaults.
For advanced use cases, you can also override input settings. See Override input settings.
When you specify a setting at the command line, remember to prefix the
setting with the module name, for example, cyberarkpas.audit.var.paths
instead of audit.var.paths.
-
var.input -
The input to use. One of
tcp(default),udporfile. -
var.syslog_host -
The address to listen to UDP or TCP based syslog traffic. Defaults to
localhost. Set to0.0.0.0to bind to all available interfaces. -
var.syslog_port -
The port to listen for syslog traffic. Defaults to
9301.
Ports below 1024 require Filebeat to run as root.
-
var.ssl -
Configuration options for SSL parameters to use when acting as a server for
TLSprotocol. See SSL server configuration options. for a description of the available sub-options. -
var.preserve_original_event -
Set to
trueto store the original syslog message under theevent.originalfield. Defaults tofalse. -
var.paths -
An array of glob-based paths that specify where to look for the log files. All
patterns supported by Go Glob
are also supported here. For example, you can use wildcards to fetch all files
from a predefined level of subdirectories:
/path/to/log/*/*.log. This fetches all.logfiles from the subfolders of/path/to/log. It does not fetch log files from the/path/to/logfolder itself.
This setting is only applicable when file input is configured.
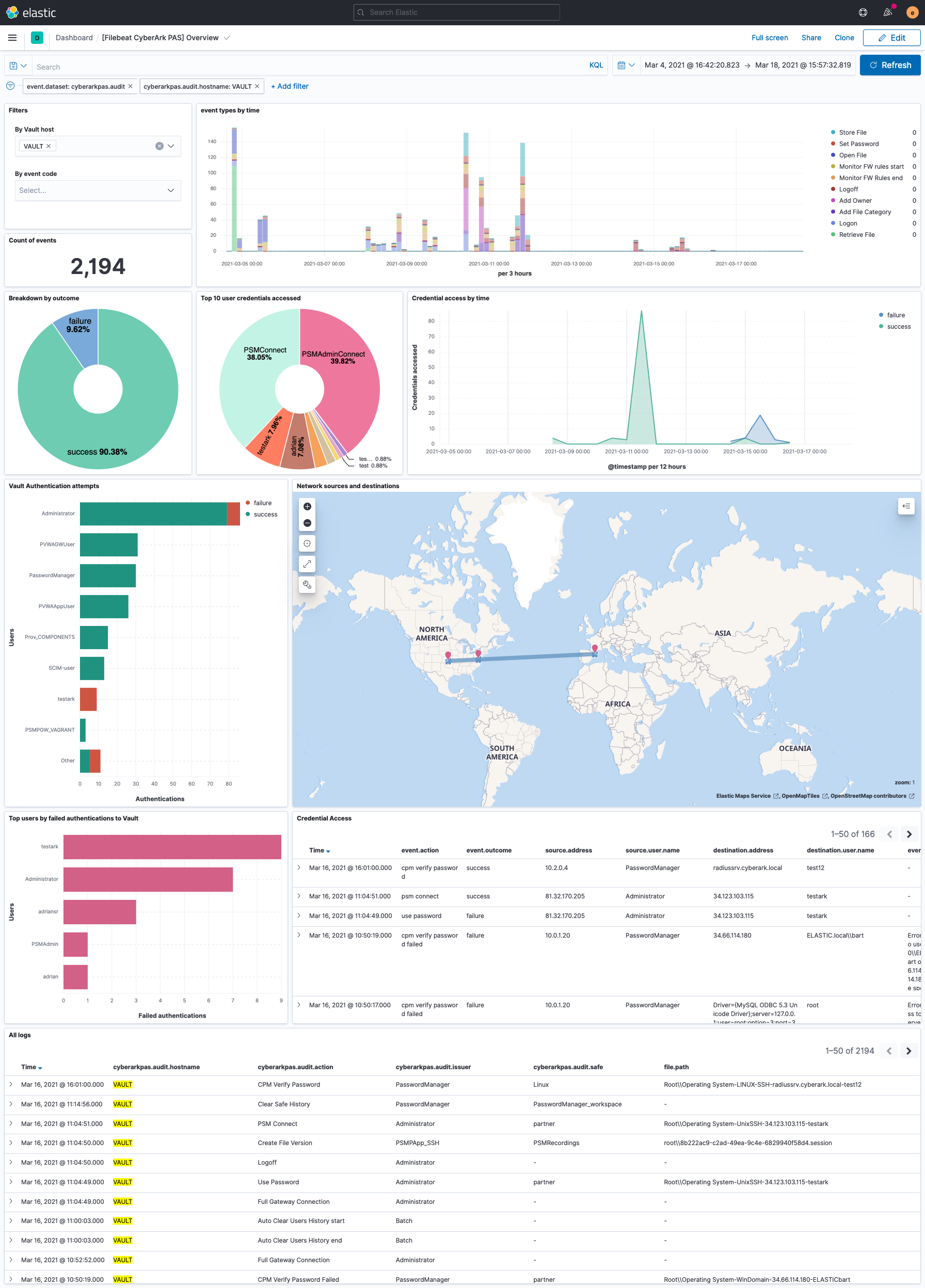
Example dashboard
editThis module comes with a sample dashboard:
Fields
editFor a description of each field in the module, see the exported fields section.