Ingest data to Elastic Security
editIngest data to Elastic Security
editTo ingest data, you can use:
- The Elastic Agent with the Elastic Endpoint Integration, which protects your hosts and sends logs, metrics, and endpoint security data to Elastic Security (see Configure and install the Elastic Endpoint integration).
- Beats shippers installed for each system you want to monitor.
- Elastic Agent to send data from Splunk to Elastic Security (see Ingest data from Splunk).
- Third-party collectors configured to ship ECS-compliant data. Elastic Security ECS field reference provides a list of ECS fields used in Elastic Security.
If you use a third-party collector to ship data to Elastic Security, you must
map its fields to the Elastic Common Schema (ECS). Additionally,
you must add its index to the Elastic Security indices (Kibana →
Stack Management → Advanced Settings → securitySolution:defaultIndex).
Elastic Security uses the host.name ECS field as the
primary key for identifying hosts.
The Elastic Agent with the Endpoint Security Integration ships these data sources:
- Process - Linux, macOS, Windows
- Network - Linux, macOS, Windows
- File - Linux, macOS, Windows
- DNS - Windows
- Registry - Windows
- DLL and Driver Load - Windows
- Security - Windows
Install Beats shippers
editTo populate Elastic Security with hosts and network security events, you need to install and configure Beats on the hosts from which you want to ingest security events:
- Filebeat for forwarding and centralizing logs and files
- Auditbeat for collecting security events
- Winlogbeat for centralizing Windows event logs
- Packetbeat for analyzing network activity
You can install Beats using the Kibana UI guide or directly from the command line.
Install Beats using the Kibana UI guide
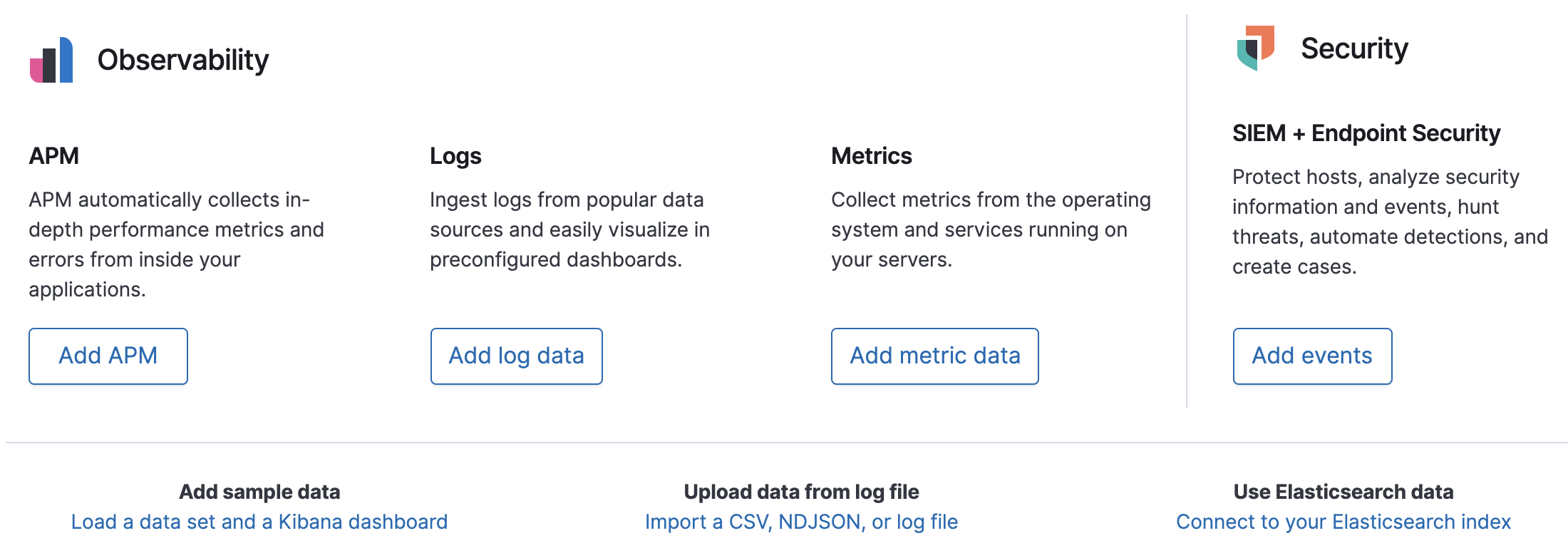
editClick Home → Add events, and follow the links for the types of data you want to collect.
Download and install Beats from the command line
editTo install Beats, see these installation guides:
Enable modules and configuration options
editNo matter how you installed Beats, you need to enable modules in Auditbeat and Filebeat to populate Elastic Security with data.
For a full list of security-related beat modules, click here.
To populate Hosts data, enable these modules:
-
Auditbeat system module - Linux, macOS, Windows:
- packages
- processes
- logins
- sockets
- users and groups
- Auditbeat auditd module - Linux kernel audit events
- Auditbeat file integrity module - Linux, macOS, Windows
- Filebeat system module - Linux system logs
- Filebeat Santa module - macOS security events
- Winlogbeat - Windows event logs
To populate Network data, enable Packetbeat protocols and Filebeat modules: